Converting a PC to a pfSense Router to Test OpenVPN Performance
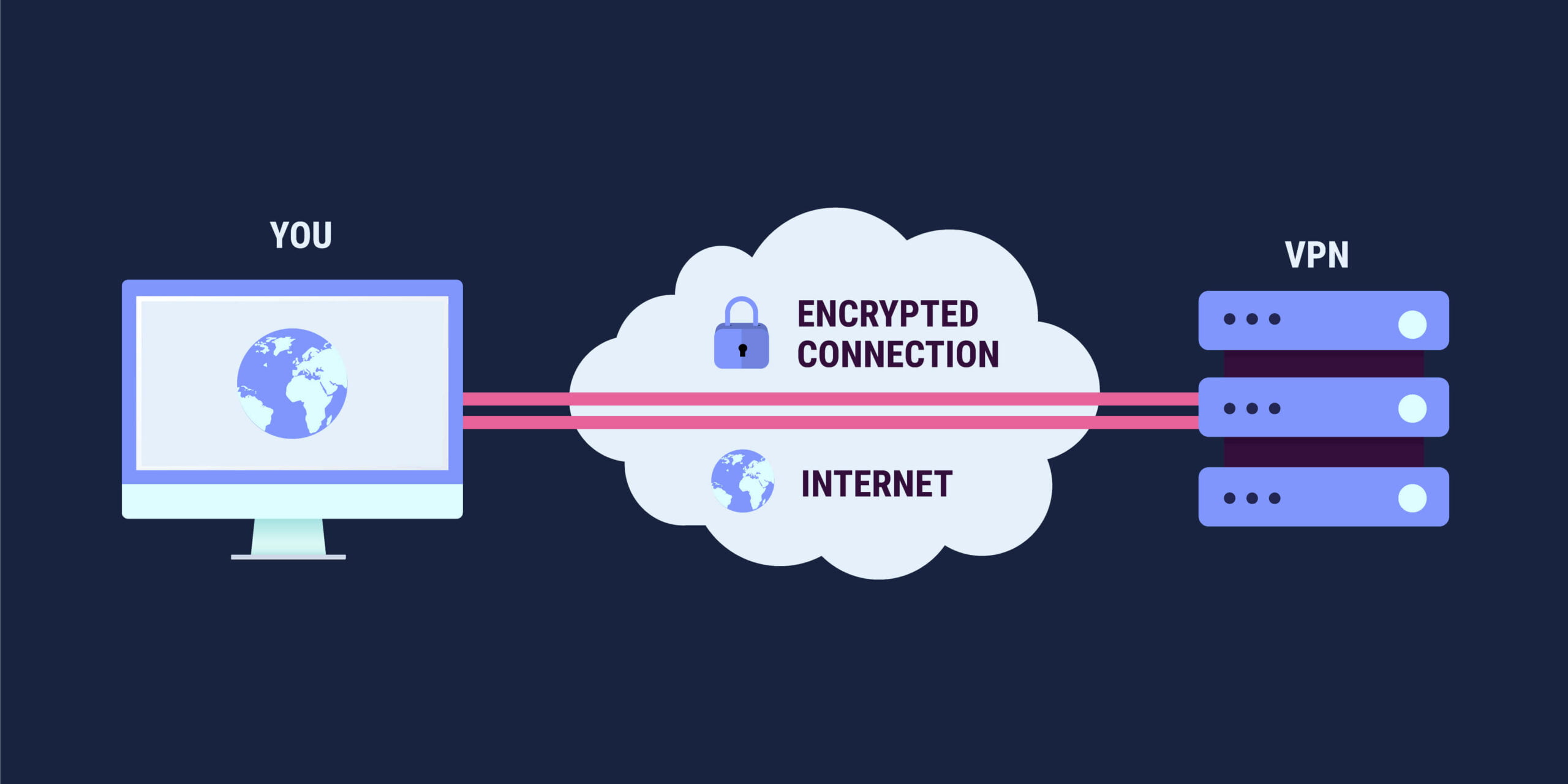
As an expat living overseas, a VPN not only provides me an additional layer of security and privacy, it also allows me to circumvent location restricted streaming media content from my home country. However, as most OpenVPN users have discovered, the CPUs inside consumer grade routers struggle in their ability to process the encryption algorithms. Further constraining OpenVPN performance is the lack of multi core threading support in the OpenVPN architecture. The result is a degradation of upload and download speeds when compared to native WAN performance.
A web search for “poor OpenVPN performance” will give you an idea of how prevalent the problem is. One recommendation is to obtain an enterprise grade router and install pfSense on it. pfSense® software is a free, open source customized distribution of FreeBSD specifically tailored for use as a firewall and router that is managed via a web interface. It also includes a long list of features and a package system that further extends the capabilities.
However, pfSense by itself is not enough. pfSense needs to be installed on a platform with an Intel® CPU that supports AES-NI. Intel® AES New Instructions (Intel® AES NI) is an encryption instruction set that improves on the Advanced Encryption Standard (AES) algorithm and accelerates the encryption of data. AES-NI is a requirement with the upcoming pfSense 2.5 release. For more information about the requirement, refer to the Netgate blog post here.
Fortunately, you do not have to spend a small fortune on an enterprise grade router to take advantage of AES-NI. If you have an older PC in your stable with an Intel processor, chances are it already supports AES-NI.
I had been keeping my eyes open for a PC to become available that had a CPU with AES-NI support. I wanted to flash it with pfSense to see how OpenVPN performance compared with my Asus RT-AC88U. Eventually, I was able to obtain a Windows 7 PC with an Intel i5-3450 CPU @ 3.10GHz x 4 cores with AES-NI.
When converting a PC to a pfSense appliance, you need two Network Adapters – one for the WAN port and one for the LAN port. All I needed to do was purchase another Network Adapter. I was able to obtain one for $12.00 at a local computer shop. I installed pfSense using the instructions on the TurboFuture website. Configuring pfSense was easy. I used the XML configuration backup file from my old pfSense appliance with an Intel Atom D525. The remaining task I had to perform to complete the setup was to install the pfBlockerNG package. pfBlockerNG is a package I use to block advertisements, dangerous domains and for my selective routing requirements. I use a D-Link 880L flashed with DD-WRT as the Wi-Fi Access Point.
For the tests below, I connected to a TorGuard VPN Server on the west coast of the USA from my home in SE Asia using a 200 Mbps fiber connection.
I was very happy with the increase in performance, especially when using an Ethernet connection. The other surprise is the difference between Ethernet and wireless performance.
For the first test, I used the Network Analyzer iOS Pro App available in the iTunes Store on my iPad to test OpenVPN performance. The speeds are in Mbps using the average of three measurements.
| Speed | pfSense 5Ghz | AC88U 5Ghz | pfSense 2.4 Ghz | AC88U 2.4 Ghz |
|---|---|---|---|---|
| Average Down | 78.96 | 21.3 | 28.3 | 22.63 |
| Average Up | 9.34 | 3.64 | 4.03 | 4.97 |
For the next test, I used the speed test feature available on the website dslreports.com. This time, I compared the difference between Ethernet and 5 Ghz Wi-Fi performance. The speeds are in Mbps using the average of three measurements.
| Speed | pfSense Ethernet | AC88U Ethernet | pfSense 5 Ghz | AC88U 5 Ghz |
|---|---|---|---|---|
| Average Down | 70.8 | 10.68 | 36.6 | 7.5 |
| Average Up | 102.17 | 6.94 | 27.46 | 5.04 |
OpenSSL Performance Tests
Around the same time I converted the PC to a pfSense router, Asus had just released the RT-AC86U router, which also had AES-NI support. Asus provided the author of Asuswrt-Merlin, Eric Sauvageau, with a model for testing. Eric posted the results of the OpenSSL speed test he ran on snbforums.com The command needs to be run from the Linux command line using an SSH session. The syntax is openssl speed –evp aes-128-cbc. This resulted in an interesting discussion on the thread I posted about my pfSense build. Following is the summary of the OpenSSL speed test metrics forum members posted for comparison purposes.
| Platform | Cipher | 16 bytes | 64 bytes | 256 bytes | 1024 bytes | 8192 bytes |
|---|---|---|---|---|---|---|
| Merlin (AC86U @ 1.8GHz) | aes-128-cbc | 187611.30k | 531473.32k | 964847.62k | 1239431.79k | 1354129.33k |
| Pfsense 2.4.2_1 (Intel i5-3450 CPU @ 3.10GHz) | aes-128-cbc | 597801.69k | 636183.39k | 647831.74k | 648930.30k | 649004.51k |
| opnsense (Intel N3700 @ 1.6GHz) | aes-128-cbc | 200326.87k | 322785.00k | 384672.70k | 405475.07k | 411444.68k |
| pfsense (Intel Core2 DUO E4600 @ 2.4GHz) | aes-128-cbc | 90379.12k | 103593.85k | 108091.19k | 108606.46k | 109062.80k |
| LTS Fork (Asus AC68P @ 1200MHz - overclock) | aes-128-cbc | 36018.40k | 41274.95k | 43366.49k | 43291.23k | 44250.54k |
| pfSense 2.4.2_1 - Netgate SG-2440 (Intel Rangeley C2358 @ 1.74GHz) | aes-128-cbc | 34722.97k | 155002.76k | 702903.75k | 3514848.60k | 10336263.02k |
However, as snbforums.com member @sfx2000 noted in this thread, OpenSSL is only one part of OpenVPN performance, it doesn’t take into account the OpenVPN application, or the HMAC, which is a specific type of message authentication code (MAC) involving a cryptographic hash function and a secret cryptographic key. According to @sfx2000, these metrics are more relevant for real-world expectations of what an end-point can do; it is up to one’s internet connection after that. So, for comparing OpenVPN performance, the following benchmark test should be used instead.
openvpn --genkey --secret /tmp/secret
time openvpn --test-crypto --secret /tmp/secret --verb 0 --tun-mtu 20000 --cipher aes-256-cbcThis generates a temporary key that will not conflict with your primary key configuration. It then asks OpenVPN to run a load of packets thru the OpenVPN application. To give the execution time in seconds a real-world meaning, apply the formula:
( 3200 / execution_time_seconds ) = Projected Maximum OpenVPN Performance in MbpsThe projected speed should be an upper limit under optimum conditions.
The magic number of 3200 comes from summing 1 to 20000, multiply by 2 for encrypt and decrypt and by 8 bits/byte and divide by 1,000,000 for a result of Mbps.
Using the example provided by @sfx2000, an Intel J1800 (Baytrail-D @ 2.41GHz) on Ubuntu 16.04LTS results in the following output:
openvpn --genkey --secret /tmp/secret
time openvpn --test-crypto --secret /tmp/secret --verb 0 --tun-mtu 20000 --cipher aes-256-cbc
real 0m18.405s
user 0m18.420s
sys 0m0.012sUsing the formula above, this gives us 3200/18.405 = 173.87 Mbps max throughput over OpenVPN.
Other forum members participating in the thread contributed their metrics as well, which are summarized below:
Asuswrt-Merlin John’s Fork AC68P overclock to 1200 MHz
AES-128-CBC: 3200/45.24 = 70.73 Mbps
AES-256-CBC: 300/48.57 = 65.88 MbpspfSense Intel i5-3450 x 4 cores AES-NI
AES-128-CBC: 3200/9.18 = 348.58 Mbps
AES-256-CBC: 3200/9.33 = 342.97 Mbps
AES-128-GCM: 3200/8.54 = 374.70 MbpsKaby Lake NUC Intel i5 7260
AES-128-CBC: 3200/3.52 = 909 Mbps
AES-256-CBC: 3200/3.59 = 891 Mbps
AES-128-GCM: 3200/2.95 = 1084 Mbps
AES-256-GCM: 3200/2.99 = 1070 MbpsAC68P @ 1200 MHz overclock
AES-128-CBC: 3200/43.22 = 74.04 Mbps
AES-256-CBC: 3200/46.94 = 68.17 MbpsOpnSense Intel N3700 @ 1.6 GHz
AES-128-CBC: 3200/22.52 = 142.10 Mbps
AES-256-CBC: 3200/23.06 = 138.79 MbpsUbuntu 16.04LTS N3700 Intel NUC box
AES-128-CBC: 3200/12.16 = 263.16 Mbps
AES-256-CBC: 3200/12.47 = 256.61 MbpsIPFire i3 7100T @ 3.4 GHz 35w
AES-256-CBC: 3200/3.903 = 819 MbpsAsuswrt-Merlin RT-AX88U @ 1.88 GHz
AES-128-GCM: 3200/2.71 = 1181 Mbps
AES-256-CBC: 3200/3.21 = 996 MbpsConclusion
The OpenSSL performance tests can give some idea of relative performance. Getting a baseline comparison across different platforms can also provide an idea of what to expect or not to expect out of a specific CPU. Other factors also have an impact, such as machine architecture efficiency and bandwidth across different buses. The Ethernet card and drivers can also play a small factor in performance, as well as the speed of the internet connection one is using. One item we can conclude from these tests is the GCM cipher, which became available in OpenVPN 2.4, now replaces the CBC cipher as the go to cipher to use for speed and performance.